Hi,
I’ve been thinking about the possibility of creating a truly distributed site in today’s bleeding edge software stack. Everything that requires a single entry point to run form is something i discard, just because that’s the very thing i try to avoid in going distributed.
In lots of today’s “distributed” sites there still seems to be some form of centralized need making it not fully distributed. Now when using web addresses and having one point, a name, to access it is a given. But that should imho be the only “centralized” point of entry.
In this post i’d like to focus on one seemingly tiny but highly important step in going distributed that at the moment just doesn’t seem to be a possibility yet. Or not to me yet, but perhaps i’m totally wrong  .
.
WebAuthn
If you don’t know what it is, it’s basically the future of passwordless login systems where something you have (your phone, a key, …) proves that you are who you are and allows you to login.
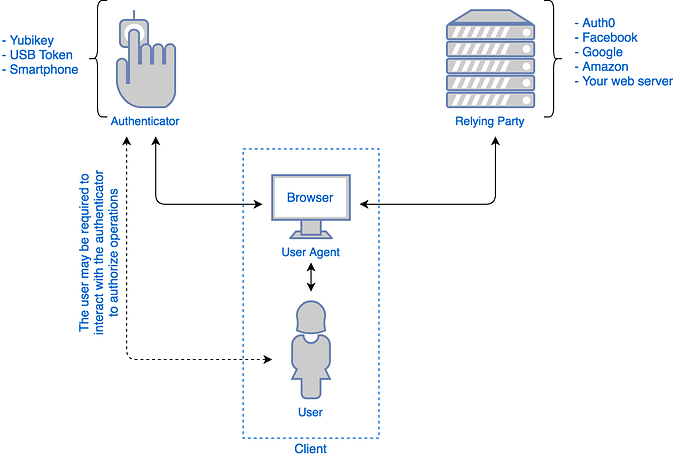
A flow of how it establishes that fact is represented in the image below (stolen from here, read it for a much more in depth article about what WebAuthn is)
As you can see in the image, there is a connection with some service (a relaying party) that hands you a challenge to solve. Overly simplified, if your device returns an answer that can be verified by your public key then you’ve proven to be who you claim you are and are logged in.
If you were to make a website you need to have something running that verifies who you claim you are. You need to have a “relaying party” on your server that takes care of that for you. Now this is where i see some issues with IPFS in it’s current form and this authentication method. This simply cannot be done. Yet. Right?
Relaying party as IPFS service?
As you can see above, “something” needs to generate random data. That “something” also needs to verify your response. Those two things can’t be done in a static environment, which IPFS is. The only way i can see this being possible is having some flag in IPFS to enable a “relaying party” service (much the same way that you can also turn pubsub on to be part of that network). This in turn means that not only “i” can verify, using the relaying party, that i am who i claim to be. But anyone with the relaying party flag turned on should be able to. Thus in effect creating a distributed relaying party network. This implicitly also means that my public key must known at any given relaying party. Now, that might be as simple as “ipfs relay-party verify <challenge> <cid>” where to cid would point to a file that would be my public key. The challenge could also be a cid pointing to a file.
Authentication in IPFS?
So how would one go about authentication on IPFS? Preferably in WebAuthn. But we can take this concept to be more abstract. In it’s core functionality i need to be able to prove that i have the key i claim to have which the other can verify with my public key. This is basically Public-Private Key Cryptography. But how does one apply that logic in IPFS to create an actual authentication system? I can think of a few ways.
#1 IPFS <crypto> command?
No, there is no such command 
I looked over the manual and there don’t seem to be any cryptography options in the IPFS cli. But then again, would that be needed, like, at all? There are whole javascript libraries out there that can do the encryption. So when going for a authentication framework, that might be the way to go?
On the other hand, having build in crypto solutions in IPFS does allow for the basic functionality to be provided from IPFS as opposed to javascript libraries.
#2 authentication framework inside IPFS
This is very much related the above one. Only then focused on authentication specifically where IPFS would support a few that can then be used in a fully distributed manner. It could still be something like ipfs auth webauthn <challenge> <public key> … I think this would be rather specific. It might work for as long as the (in this case) webauthn standard lives, but would need to be updated over time. It might also complicate looking at sites via IPFS gateways where one gateway might have a newer authentication protocol then another one. Leading to a mess you probably don’t want.
So,. just throwing this out here to see if there are more opinions on this.
Remember, the eventual goal is a fully decentralized authentication or the raw components to make that!
Cheers,
Mark